Doorways … The linking between your memory frames
Happy New Year everyone and welcome to 2015. I had planned to write about this last year (like many things planned 🙂 ), however yesterday as I searched my house for something I suddenly remembered and thought I would do it a...
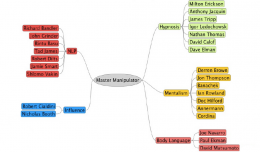
Improve Your Social Engineering Skills… Master Manipulator Mind Map
In my talk Head Hacking – The Magic of Suggestion and Perception, I talk about the best type of Social Engineer, this is the Master Manipulator. Many people have these skills naturally, but may not be consciously aware of...
Subliminal Hacking at IRISSCERT Cyber Crime Conference … Ireland Security Conference
I have the great pleasure of speaking at the 2011 IRISSCERT Cyber Crime Conference in Ireland this November. IRISSCERT Cyber Crime Conference The IRISSCERT Cyber Crime Conference will be held this year on Wednesday the 23rd of ...
Quick Post – More Illusions … Of the 3D Printed Variety
Loving illusions again at the moment, and found a couple that I could print on my 3D Printer, so I put it to work and here are the results, how you enjoy.
Body Talk… Arms out rah rah rah
Hope everyone is off to a good week, what with Defcon, Blackhat etc I am sure many of you are travelling. I personally had a weekend break in Cardiff and enjoyed doing a little grey matter manipulation, as well as talking about...