Text Message Scammers … ID Theft Attempt & Run
Thought I would share some info on a text scam I got a few weeks ago. I setup a fake email account, got a burner number to make relevant calls and generated fake name, address, card number etc to see how these guys would respon...
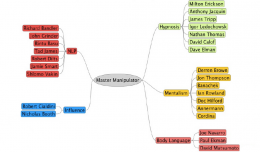
Improve Your Social Engineering Skills… Master Manipulator Mind Map
In my talk Head Hacking – The Magic of Suggestion and Perception, I talk about the best type of Social Engineer, this is the Master Manipulator. Many people have these skills naturally, but may not be consciously aware of...
Welcome to Head Hacker
Welcome and thanks for visiting the Head Hacker website. The goal of this site is to discuss the benefits, process, theories and qualities associated with social engineering, and what I consider to be linked skills, products an...
Just Called To Say … Spoofed Your Caller ID
The aim of this post is to share tools for Social Engineers to include vishing in you engagements, and to make the rest of the world aware of just how simple and easy it is to Spoof someones Caller ID, so you can increase your ...
Hypnosis… Mumbo Jumbo or the Real Thing
Next lets look at Hypnosis. I am sure everyone is familiar with the term hypnosis, and we all have our own conception of what hypnosis is. Of course we are all entitled to our own opinions and views, and many will simply dismis...