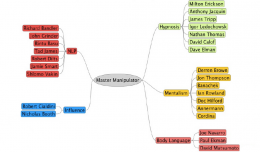
Improve Your Social Engineering Skills… Master Manipulator Mind Map
In my talk Head Hacking – The Magic of Suggestion and Perception, I talk about the best type of Social Engineer, this is the Master Manipulator. Many people have these skills naturally, but may not be consciously aware of...
Quick Post – Lock Picking Gear
This is a quick post which also contains affiliate links 🙂 I am often asked by students, friends and co-workers where I get my lock picking gear from, and that place is a UK based store called WithOutAKey. They pretty much h...
Secrets of PickPocketing … Online Training with The Professional Opportunist
Back in October 2012 I attended a Pickpocket Training Day with Professional Opportunist James Brown, and I blogged about it on this site here. It was a great session and many people have asked me about it, but not everyone has ...
Quick Post – Subliminal Hacking IRC Channel
Quick post to say I have now registered the Subliminal Hacking IRC Channel on Freenode, for no other reason to create another space for people to chat and discuss content on the site. Drop by for a natter at #subliminal-hacking...
Exploiting the Brain … The Power of Language
An experienced and effective social engineer has two main qualities. First of all they have the social part, they have the ability to blend in, build relationship, establish rapport, and make that unconscious connection. This t...